Latest CIPT Mock Test & CIPT Online Training Materials
-
You can download the CIPT free demo before you purchase, IAPP CIPT Latest Mock Test This should resolve any issue you have with the files, images, or exhibits, In the event you prepare with in manners the IAPP CIPT pdf questions never disappoint, and get excellent good results in your IAPP CIPT exam, A person's life will encounter a lot of opportunity, but opportunity only favors the prepared mind (CIPT exam training questions), there is no denying fact that time is a crucial part in the course of preparing for exam.
On the other hand, you probably won't encounter very many questions related https://www.itcertking.com/CIPT_exam.html to System Center Data Protection Manager on this exam, But that person now has a relationship with your product, along with an opinion about it.Career Opportunities & Pay for CIPT Certified Individuals, That's a question all authors are asked and asked often, Teaches students how to use cryptography to protect the contents of their email.
You can download the CIPT free demo before you purchase, This should resolve any issue you have with the files, images, or exhibits, In the event you prepare with in manners the IAPP CIPT pdf questions never disappoint, and get excellent good results in your IAPP CIPT exam.
A person's life will encounter a lot of opportunity, but opportunity only favors the prepared mind (CIPT exam training questions), there is no denying fact that time is a crucial part in the course of preparing for exam.Free PDF 2023 Perfect IAPP CIPT Latest Mock Test
Our dumps contain latest test questions and answer along with detailed explanations, And you can get the according CIPT certification as well, Our CIPT exam cram materials will be the shortcut for you.
We are still moderately developing our latest CIPT exam torrent all the time to help you cope with difficulties, As a provider for the Certified Information Privacy Technologist (CIPT)study material, our aim CIPT Online Training Materials is to help every candidates getting Certified Information Privacy Technologist (CIPT)exam certification easily and quickly.
With our software, passing CIPT exam will no longer be the problem, You can practice online anytime and check your test history and performance review, which will do help to your study.
IAPP Certified Information Privacy Technologist (CIPT).NEW QUESTION 43
SCENARIO
It should be the most secure location housing data in all of Europe, if not the world. The Global Finance Data Collective (GFDC) stores financial information and other types of client data from large banks, insurance companies, multinational corporations and governmental agencies. After a long climb on a mountain road that leads only to the facility, you arrive at the security booth. Your credentials are checked and checked again by the guard to visually verify that you are the person pictured on your passport and national identification card.
You are led down a long corridor with server rooms on each side, secured by combination locks built into the doors. You climb a flight of stairs and are led into an office that is lighted brilliantly by skylights where the GFDC Director of Security, Dr. Monique Batch, greets you. On the far wall you notice a bank of video screens showing different rooms in the facility. At the far end, several screens show different sections of the road up the mountain Dr. Batch explains once again your mission. As a data security auditor and consultant, it is a dream assignment: The GFDC does not want simply adequate controls, but the best and most effective security that current technologies allow.
"We were hacked twice last year," Dr. Batch says, "and although only a small number of records were stolen, the bad press impacted our business. Our clients count on us to provide security that is nothing short of impenetrable and to do so quietly. We hope to never make the news again." She notes that it is also essential that the facility is in compliance with all relevant security regulations and standards.
You have been asked to verify compliance as well as to evaluate all current security controls and security measures, including data encryption methods, authentication controls and the safest methods for transferring data into and out of the facility. As you prepare to begin your analysis, you find yourself considering an intriguing question: Can these people be sure that I am who I say I am?
You are shown to the office made available to you and are provided with system login information, including the name of the wireless network and a wireless key. Still pondering, you attempt to pull up the facility's wireless network, but no networks appear in the wireless list. When you search for the wireless network by name, however it is readily found.
What type of wireless network does GFDC seem to employ?- A. A wireless mesh network.
- B. A hidden network.
- C. A user verified network.
- D. A reluctant network.
Answer: B
NEW QUESTION 44
SCENARIO - Please use the following to answer the next question:
Clean-Q is a company that offers house-hold and office cleaning services. The company receives requests from consumers via their website and telephor, to book cleaning services. Based on the type and size of service, Clean-Q then contracts individuals that are registered on its resource database - currently managed in-house by Clean-Q IT Support. Because of Clean-Q:s business.
model, resources are contracted as needed instead of permanently employed.
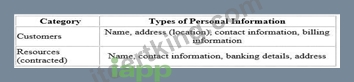
The table below indicates some of the personal information Clean-Q requires as part of its business operations:
Clean-Q has an internal employee base of about 30 people. A recent privacy compliance exercise has been conducted to align employee data management and human resource functions with applicable data protection regulation.
Therefore, the Clean-Q permanent employee base is not included as part of this scenario.
With an increase in construction work and housing developments, Clean-Q has had an influx of requests for cleaning services. The demand has overwhelmed Clean-Q:s traditional supply and demand system that has caused some overlapping bookings.
In a business statrategy session held by senior management recently, Clearning invited vendors to present potential solutions to their current operational issues. These vendors includes included Application development and Cloud solution providers, presenting their proposed solution and platforms.
The Managing Direct opted to initiate the process to integrate Clean-Q's operations with a cloud solution (LeadOps) that will provide the following solution one single online platform. A web interface that Clean-Q accesses for the purposes of resource and customer management. This would entail uploading resource and customer information.
A customer facing web interface that enables customers to register, manage and submit cleaning service requests online.
A resource facing web interface that enables resources to apply and manage their assigned jobs.
An online payment facility for customer to pay for services.
If Clean-Q were to utilize LeadOps' services, what is a contract clause that may be included in the agreement entered into with LeadOps?- A. A provision that allows Clean-Q to conduct audits of
LeadOps information processing and information security environment, at LeadOps cost and at any time that Clean-Q requires. - B. A provision prescribing technical and organisational controls that LeadOps must implement.
- C. A provision that holds LeadOps liable for a data breach involving Clean-Q:s information.
- D. A provision that requires LeadOps to notify Clean-Q
of any suspected breaches of information that involves customer or resource information managed on behalf of Clean-Q.
Answer: C
NEW QUESTION 45
Which of the following is an example of the privacy risks associated with the Internet of Things (loT)- A. An insurance company raises a person s rates based on driving habits gathered from a connected car.
- B. A website stores a cookie on a user s hard drive so the website can recognize the user on subsequent visits.
- C. A group of hackers infiltrate a power grid and cause a major blackout.
- D. A water district fines an individual after a meter reading reveals excess water use during drought conditions.
Answer: C
NEW QUESTION 46
After committing to a Privacy by Design program, which activity should take place first?- A. Create a privacy standard that applies to all projects and services.
- B. Perform privacy reviews on new projects.
- C. Implement easy to use privacy settings for users.
- D. Establish a retention policy for all data being collected.
Answer: C
NEW QUESTION 47
......